The GWDC is proud to present this event with our partners: ISACA GWDC, along with our partners are proud to host our annual Women in Leadership and Technology Special Event. This year's theme is "AI, Cybersecurity, and Audit Leadership: Pioneering Change." This is a distinguished and empowering gathering … [Read more...] about Women in Leadership and Technology 2024 Special Event
Security and Risk Trends – Recap of 2023 with a Look ahead to 2024
The ISACA Greater Washington DC (GWDC) proudly hosts the 2023 Security and Risk Trends conference. This seminar will recap cybersecurity and risk trends noted/experienced in 2023 and look ahead to what to expect in 2024. This virtual conference is part of our monthly conference series. Business leaders and managers, … [Read more...] about Security and Risk Trends – Recap of 2023 with a Look ahead to 2024
CISA Spring 2024 Review Course
The GWDC is sponsoring an intensive 4-day virtual review course for the Certified Information System Auditor® (CISA®) exam. This review course will provide practical advice on preparing for the CISA exam and specific instruction regarding the job practice areas addressed by CISA as defined by ISACA® Global. The dates of … [Read more...] about CISA Spring 2024 Review Course
Cybersecurity 2023 Conference
The GWDC is proud to host its annual cybersecurity conference. This virtual conference is part of our monthly conference series. Business leaders and managers, executives, technologists, professionals, and students, interested in staying current in the field of cybersecurity should attend this conference. Registration … [Read more...] about Cybersecurity 2023 Conference
CISA Fall 2023 Review Course
The GWDC is sponsoring an intensive 4-day virtual review course for the Certified Information System Auditor® (CISA®) exam. This review course will provide practical advice on preparing for the CISA exam and specific instruction regarding the job practice areas addressed by CISA as defined by ISACA® Global. The dates of … [Read more...] about CISA Fall 2023 Review Course
Summer Seminar – Cybersecurity
Organizations face complex cybersecurity challenges and need to prepare in addressing current and future cybersecurity risks, protection of operations and sensitive data, and compliance with regulatory requirements. Join ISACA Greater Washington DC and Guidehouse for this summer seminar and don’t miss this opportunity to … [Read more...] about Summer Seminar – Cybersecurity
Women in Technology and Leadership Conference 2023
The ISACA GWDC Chapter is proud to host our 2023 Women in Technology and Leadership Conference. This conference is our premier annual event centered around the experience of women in technology and leadership positions. Our technology enrichment topics will focus on awareness and strategies around Cybersecurity, Data … [Read more...] about Women in Technology and Leadership Conference 2023
Certificate of Cloud Auditing Knowledge (CCAK™) Spring 2023 Review Course
The GWDC is sponsoring an intensive 3-day virtual review course for the Certificate of Cloud Auditing Knowledge (CCAK™). The dates of the CCAK review course are three consecutive Saturdays: May 6, 13, and 20, 2023 from 8:30 am to 5:00 PM. The CCAK course is designed to cover the following five core areas of focus: Cloud … [Read more...] about Certificate of Cloud Auditing Knowledge (CCAK™) Spring 2023 Review Course
CISA Spring 2023 Review Course
The GWDC is sponsoring an intensive 4-day virtual review course for the Certified Information System Auditor® (CISA®) exam. This review course will provide practical advice on preparing for the CISA exam and specific instruction regarding the job practice areas addressed by CISA as defined by ISACA® Global. The dates of … [Read more...] about CISA Spring 2023 Review Course
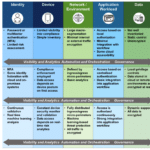
White House Releases Draft Federal Zero Trust Strategy
If you're interested in cybersecurity, check out our 2021 Cybersecurity Conference or one of our cyber-focused training or certification options. Will we talk about the draft Federal Zero Trust Strategy? Tune in to find out. This week, the White House released their Federal Zero Trust Strategy to help agencies comply … [Read more...] about White House Releases Draft Federal Zero Trust Strategy